
For the better part of modern human history, people have been devising new and inventive ways to swindle others out of their money. In the past, these scams were limited to the small audience that the con artist could reach. Today, it’s easy to reach anyone through a computer, and the schemes are constantly evolving. We may have gotten wiser since the “Nigerian Prince” email days, but that doesn’t mean that we’re immune to scams we’ve never heard of. Forewarned is forearmed, so here’s just some of the most common ways you could get tricked into handing over your money online.
E-cards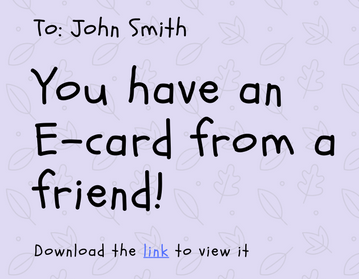
You’ve probably received one of these around your birthday or a major holiday, usually from a well-meaning relative. The bright graphics and audio can make it tempting to click on, but e-cards are one of the ways that scammers can exploit even the most innocuous of messages. Sure, a real e-card sent by someone you know and trust is one thing, but what about e-cards from people you don’t know? Or, in an even more insidious twist, when scammers may use your friend’s email to forward their e-card message to everyone in their address book. This kind of e-card can be difficult to identify as fake, because it comes from someone you know.
Some ways to identify an E-card as fake:
-There are spelling and grammatical mistakes in the card. The sort of companies that will ask you for sensitive information (such as banks, creditors, or utilities) are unlikely to hire someone who doesn’t speak English well enough to draft their emails. It’s even more unlikely that a an e-card company (whose business model revolves around communication) would have glaring errors in the text of their messages, so if you see any of these, think before you click.
-There is an attachment in the email that has you download the e-card to view it. In general, E-card companies don’t have you download attachments in order to view your card, in fact, many will include the e-card within the body of the email. Sometimes there’s a link to view your e-card, so always inspect the link to make sure it’s legitimate before clicking on it.
-There are terms and conditions to agree to if you want to view your card. Real e-card companies won’t have you agree to terms before you can see the card you were sent. Many times, the “terms and conditions” are there to get the user to click on a link that contains malicious software. Once on your computer, the scammers can take further action against you.

Phishing
“Phishing” gets its name from how fishermen dangle bait so they can snag a fish. In the online world of phishing, scammers are the fishermen, and they send out “bait” in the form of legitimate looking websites that users can click on. An example of a phishing scam is when a scammer sends out a link saying “Urgent – Wells Fargo customers need to take action”. If you’re a Wells-Fargo customer, you might open that email. The email conveys a sense of urgency, saying that customer’s account information has been compromised. They’ll then provide a link that you click on to “verify” that your account wasn’t one of those affected. This link will take you to a legitimate looking site where you enter personal and sensitive information. This information can then be used against you in additional scams, or your credit might be affected. Here’s how to spot one of these scams:
-The email isn’t relevant to you. In the above example, the email was targeted at people who bank with Wells-Fargo. If you don’t use Wells-Fargo, it should be obvious that the email is a fake one.It can be difficult to use this method though, because we don’t always remember if we’ve been in touch with a particular company.
-The website URL is different than what it should be. Back to our example of Wells-Fargo, the site they try to direct you to will be different than the official site. The link might say “wells-fargo.com”, “wellsfargo.net”, or any other permutation of the real “wellsfargo.com”. The similarity to a real website lends an air of authenticity that some other scams fail to supply. The changes that the scammers make are sometimes so subtle that they are easy to miss and can easily fool us. Make sure to inspect the website for anything that seems out of place, or better yet, only enter information when the website is “secured”. The way to know this is to check the URL on the top of the page. If the address begins with https:// instead of http://, then you can be assured that the information you enter is safe.
-They seem to know personal information about you
Sometimes people can forget that there’s a lot of information about themselves online. Whether you post on Facebook, Instagram, or your own personal blog, there are lots of ways scammers can collect your personal information. They may use this information to their advantage by pretending to be someone they’re not, or they may threaten you with blackmail. Don’t be fooled in the heat of the moment by someone who has information about you that you thought was private. Take the time to think about how they could have obtained this information, and whether or not the information is truly sensitive. The bottom line – think before you post, and go through your social media accounts to adjust and strengthen your privacy filters.

Social Engineering
Speaking of social media, there are other ways in which scammers use social media sites to their advantage. They may create fake profiles and try to “follow” or “friend” you in order to message you. They might spam your inbox with malicious sites, or alternatively, they could try to establish a rapport to gain your trust. In any case, a mindful social media user will interact only with those people who they met and trust in real life.

Fake anti-virus
Everyone should have proper anti-virus protection installed across all their devices, but even the best antivirus can’t protect you against all threats. Sometimes, you may get a pop-up window claiming that you have “x number of viruses on your device”. The popup may even write the name of the device that you’re browsing on, which gives it a sense of authenticity. The problem is, that anti-virus scans take time. There’s no program out there that can scan your device without having been installed, and is able to know exactly how many viruses are on your computer in the time it takes to open a pop-up window. These sort of scams usually prompt you to install their own “anti-virus software” that will allegedly remove the threats that they “found”. If you install this software, you might be giving them access to install even more harmful programs on your computer.

“Tech Support” Scam
Playing off of the fake antivirus scam, sometimes a popup window will appear saying that you need to call “XXX-XXXX” in order to resolve issues with your computer. If you call, you’ll get connected to someone claiming to be tech support (like from Microsoft or Apple) and they’ll be happy to help resolve the issue with your computer. They’ll prompt you to install a remote access program such as LogMeIn to get access to your computer. Once there, they can wreak all sorts of havoc on your computer, such as shutting down anti-virus protection, or rewriting sensitive files. They could also remand payment for services rendered, and say they won’t give you access back until you do.
Some things to take away:
-Never trust a pop-up window. Though the warnings and messages they contain seem important, it’s just a way to grab your attention.
-Don’t trust a call from someone who claims to be “tech support”. A tech support service like AppleCare will help you when you reach out to them, not the other way around.
-Most importantly – don’t give remote access to anyone you don’t know! If a service technician has to access your computer remotely, make sure it’s from a verified company whose number can be checked against a verifiable online source (like the Microsoft contact page).
 Job Offer Scams
Job Offer Scams
If you’ve been looking for a new job, you’ve probably posted your resume to a few job board sites in the hope that someone would take notice. I hope real employers looked at your post, but it’s just as likely that someone looking to scam you has come across it as well. These scammers will search job board sites and offer lucrative job offers to profiles they come across. They may say that they want you to start as soon as possible at a fully online job that pays a significant amount per hour. This can be an enticing offer to a job applicant, but like the above examples, they’re just “dangling the bait”. When they say they’ve hired you for a job (after the most perfunctory of interviews), they’ll likely ask you for personal data like your social security number or banking information. Don’t give out your personal information to anyone you’ve only met online. If you’re contacted, you may also be asked to pay for training materials, background checks, or the like. A legitimate job will have specific job requirements, will likely require you to come in to have a personal interview, and will be verifiable by external resources.
These are just a few popular ways that scammers can try to gain our trust, but the world of scams is always evolving. In the future, scams may get more sophisticated and personal, so keeping a sharp eye out for suspicious activity is always a good idea.













